The Million-Download Trap: How a Trusted Open-Source Package Became a Gateway for Credential Theft
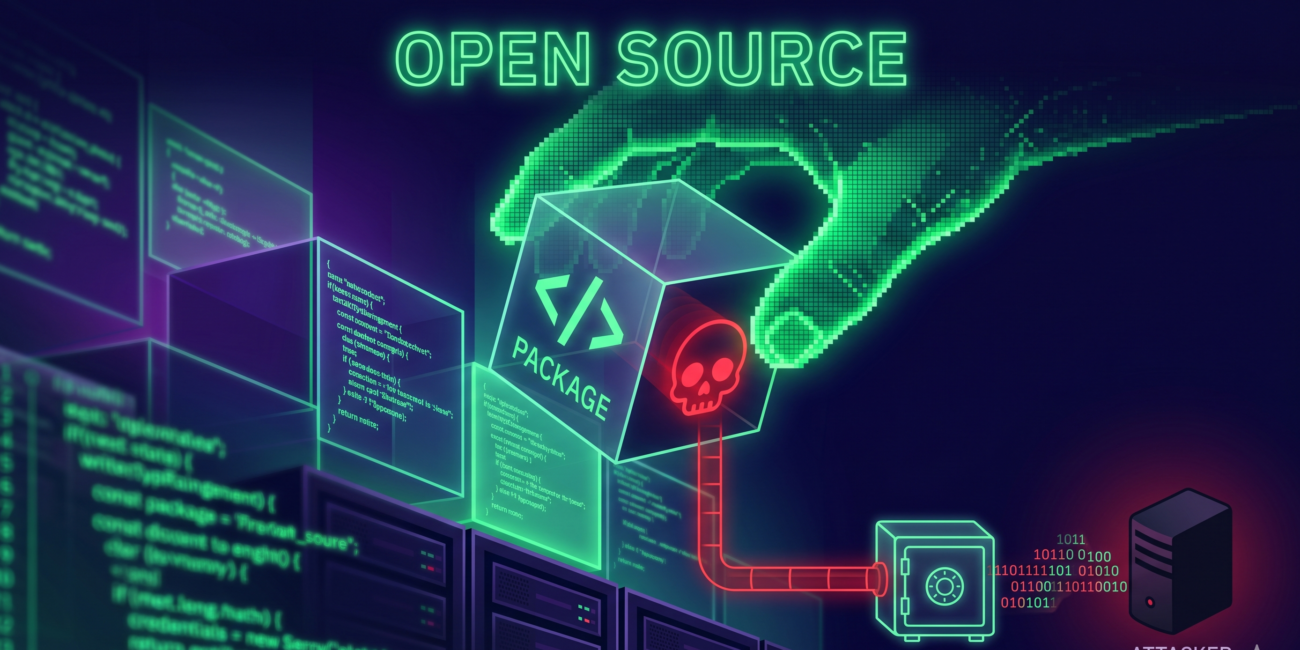
The global software development landscape has been shaken by the discovery of a sophisticated cyberattack embedded within a highly popular open-source package. Boasting an impressive reach of over one million downloads every month, the library in question was a staple for thousands of developers worldwide. However, what appeared to be a reliable tool for streamlining code was actually a Trojan horse designed to harvest sensitive user credentials and private data. This breach represents one of the most significant supply chain attacks in recent years, highlighting the extreme vulnerability of the modern digital ecosystem that relies heavily on third-party, community-maintained code.
The Deceptive Rise of a Malicious Library
The success of this attack lay in its camouflage. In the world of open-source development, high download numbers and a long history of activity are often used as shorthand for trustworthiness. This particular package managed to achieve a massive scale of distribution by offering essential functionality that developers frequently require. By appearing to be a helpful, well-maintained resource, it bypassed the initial skepticism that usually accompanies new or obscure software. The attackers leveraged a psychological loophole in the developer community: the assumption that if a tool is used by millions, it must have been thoroughly audited by someone else.
Instead of launching an immediate or obvious attack, the malicious actors behind this campaign played a long game. They ensured the package functioned exactly as advertised, providing the promised utility while secretly bundling a small, obfuscated snippet of code. This code was designed to remain dormant during automated security scans, only activating under specific conditions that mirrored a real-world production environment. This level of sophistication allowed the package to remain undetected on major repositories for an extended period, slowly infiltrating the infrastructure of small startups and massive corporations alike.
Mechanism of the Theft: The Silent Exfiltration
The technical execution of the theft was both simple and devastatingly effective. Once a developer integrated the compromised package into their application, the hidden script would initialize during the software’s runtime. Its primary objective was to scan the host system for high-value targets, specifically focusing on environment variables and local configuration files. These areas often contain the “keys to the kingdom,” such as database passwords, cloud service credentials, and API keys for platforms like AWS, Stripe, and GitHub.
Beyond just scanning files, the malware was capable of intercepting data during active user sessions. By hooking into the application’s input fields, the script could capture login credentials in plain text as users typed them. This data was then encrypted and bundled into small packets to avoid triggering network anomaly detections. These packets were periodically sent to a series of command-and-control servers masked as legitimate analytics traffic. Because the package was already a trusted part of the application’s architecture, these outbound connections often went unblocked by standard firewalls, allowing the attackers to build a massive database of stolen identities and access points.
The Crisis of the Open-Source Supply Chain
This incident brings to the forefront a critical debate regarding the security of the software supply chain. Modern applications are rarely written from scratch; instead, they are assembled like Lego sets using hundreds or even thousands of open-source dependencies. While this accelerates innovation, it creates a “nested” risk. If a single package at the bottom of the stack is compromised, every application built on top of it becomes a target. The fact that a package with a million monthly downloads could be weaponized so effectively suggests that the current peer-review system for open-source software is struggling to keep pace with the ingenuity of cybercriminals.
The attack also utilized a technique known as typosquatting and social engineering to maintain its grip. In some instances, the malicious package was named so similarly to a legitimate, famous library that developers accidentally installed the wrong one. In other cases, the attackers might have gained the trust of the original maintainers or taken over an abandoned project that already had a large user base. This manipulation of trust is what makes supply chain attacks so difficult to defend against, as the threat does not come from a “break-in” but from an “invite-in.”
Industry-Wide Fallout and the Path to Recovery
The aftermath of this discovery has sent ripples through the tech industry, forcing a massive cleanup operation. Major package repositories have moved quickly to delist the library and alert affected users, but the damage is already widespread. For organizations that had integrated this code into their production environments, the road to recovery is complex. It is not enough to simply delete the package; security teams must now assume that any credential handled by those systems has been compromised. This necessitates a total “secret rotation,” where every password, token, and key is invalidated and replaced—a process that can take weeks of manual labor and cause significant downtime.
Furthermore, this breach has triggered a wave of legal and compliance concerns. Under regulations like GDPR and other data privacy laws, companies are responsible for the security of the third-party tools they use. The realization that a “trusted” open-source tool was the source of a data leak puts many firms in a difficult position regarding liability. It highlights the urgent need for more robust software bill of materials (SBOM) practices, where companies maintain a transparent and constantly monitored list of every single piece of code entering their ecosystem.
A New Era of Digital Vigilance
As the tech community grapples with the scale of this theft, the focus is shifting toward preventative measures that go beyond simple automated scanning. Experts are calling for a move toward “Zero Trust” architectures even within the software build process. This involves treating every third-party dependency as a potential threat until proven otherwise, utilizing sandboxing techniques to isolate libraries from sensitive parts of the system, and implementing stricter monitoring of outbound network traffic from applications.
The era of blind trust in open-source popularity is effectively over. This million-download disaster serves as a stark reminder that in the digital age, convenience often comes at the cost of security. The responsibility now lies with both developers and the platforms that host these libraries to implement more rigorous verification processes. While the open-source model remains a powerful engine for global progress, its survival depends on the community’s ability to defend its infrastructure against those who would turn a shared resource into a weapon for mass surveillance and theft. Moving forward, the industry must prioritize security at the foundational level, ensuring that the libraries we rely on are as safe as they are functional.